Revil Sodinokibi Ransomware: Introduction
Revil Sodinokibi : Swascan’s Cyber Incident Response Team has observed and analysed the new ransomware family known as Sodinokibi Ransomware. The ransomware in question, also called REvil, is to be active at least as of April 2019.
Revil or Sodinokibi is one of the most active families of this type of malware, in particular through ransomware as a service (RaaS).
In practice, the Revil Group does not carry out attacks straight away.
It makes infrastructure, tools, ransomware and related code available to criminal third parties.
Under Ransomware Attack? Contact us!
The attacks are carried out by ‘clients’ – also called affiliates – and the criminal group REvil receives a percentage of the ransoms extorted from the victims (estimated at 20-30%).
This criminal ‘business model’ has allowed the spread and use of this ransomware to increase.
It is no coincidence that the Criminal Hacker group REvil claimed that the activity secured an illicit profit of more than $100 million this year alone and in 2019 an illicit profit of 8% more than the famous Ryuk ransomware despite Sodinokibi only appearing in the second quarter of last year.
Revil Sodinokibi Ransomware: Summary
The REvil Sodinokibi ransomware was intercepted and identified for the first time in April 2019. It has similarities, on a tactical level, with the GandCrab ransomware. The similarity is determined by the use of similar code.
The particularities of this ransomware are:
- Information exfiltration
- Information encryption
- Configurability; this implies the possibility of compiling, customising and optimising the payload.
- Publication of exfiltrated files in a dedicated blog in case of non-payment of the ransom.
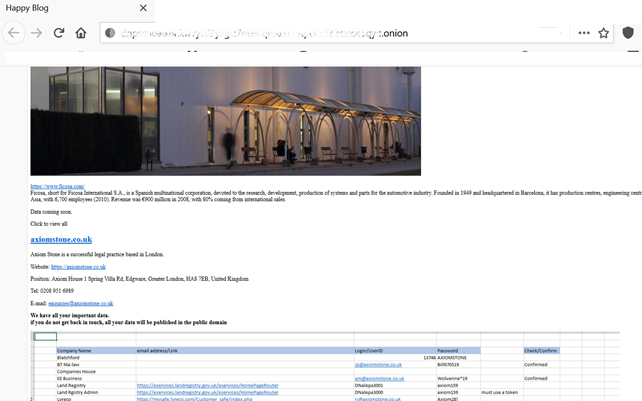
The blog where the stolen data is published
Since June, the criminal hackers of Revil have in fact created a ‘public’ auction of critical information, in terms of business and/or privacy, that has been exfiltrated. This escalation is a new lever to pressure victims into paying the ransom and at the same time a new illicit ‘profit channel’ for cybercriminals.
Sodinokibi Ransomware: Technical Details
Revil Ransomware: Decrypt files
Files encrypted by the REvil Sodinokibi ransomware are not decryptable. At the moment, there are no decryptors that can restore data in plain text. In particular, Revil uses elliptically curved Diffie-Hellman keys. A cryptographic algorithm with shorter but more effective keys.
Sodinokibi creates two different public keys, one as part of the JSON configuration and another embedded in the binary itself. These public keys will be used to encrypt the locally generated private key.
Revil Sodinokibi: Attack Vectors
The Revil Sodinokibi ransomware gains access to the target infrastructure through:
- Exploitation of known vulnerabilities
- Social Engineering and specifically phishing campaigns,
Specifically, some analyses show that the main vectors are compromised RDP sessions (65%), phishing (16%) and software vulnerabilities (8%).
Revil Sodinokibi: Exploiting vulnerabilities
Regarding the exploitation of vulnerabilities in 2019, the CVE-2019-2725 vulnerability related to Oracle Weblogic (CVE-2019-2725) was widely exploited.
In recent months, the main attack vectors are:
- Exposed RDP systems
- Fortinet VPN CVE-2018-13379
Revil: Early Warning
Cyber Security Framework systems equipped with Soc as a Service systems have the possibility of intercepting any intrusion attempts in advance. In the absence of an adequate corporate Cyber Security Framework, one of the signals of intrusion by Revil Sodinokibi is to detect the presence of terminals configured in:
- Azerbaijani Latin
- Georgian
- Tartar
- Romanian
- Azeri
- Kazakh
- Kyrgyzstan
- Turkmen
- Uzbek Latin
- Uzbek
- Ukrainian
- Russian
- Belarusian
- Tajik
- Armenian
- Syriac
- Syrian Arab
In this case, it is strongly recommended to implement a digital investigation activity through an Incident Response Team that aims to identify the presence of pyload and malicious artefacts within the corporate network.
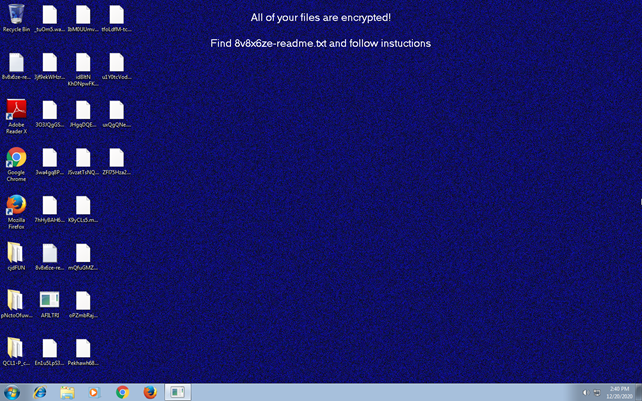
Sodinokibi Ransomware: the ransom request
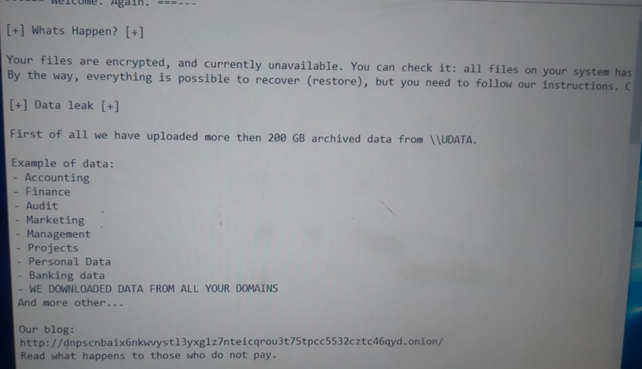
The request
Revil Sodinokibi:Exfiltrated Information – Data Breach
As indicated above REvil Sodinobiki performs data exfiltration.
The ransomware not only encrypts and/or deletes the backup files directly, but also exfiltrates company data directly. The exfiltration takes place before encryption takes place. In particular, Sodinobiki also implements sophisticated code obfuscation techniques to evade detection by antivirus software.
Specifically, Revil exfiltrates the following data:
- Files and documents
- Systems architecture
- User name
- Computer name
- Workgroup
- Operating system
- Processor information
Data encryption
Sodinokibi is ransomware that encrypts all files on local drives except those listed in their configuration file.
File extension: .java, .aaf, .aep, .aepx, .plb, .prel, .aet, .ppj, .gif .psd. .bmp, .3dm, .max, .accdb, .db, .mdb, .dwg, .dxf, .cpp, .cs, .h,, php, .asp, .rb, .jpg, .jpeg, .raw, .tif, .png.
Execution and Activities
Having gained access to the victim’s systems, it adds the following processes:
powershell.exe -e {base-64 encoded command}
It also terminates and blocks the following services:
- mepocs
- vss
- memtas
- sql
- veeam
- sophos
- backup
- svc$
On infected systems it also blocks and terminates:
- winword
- ocssd
- sql
- encsvc
- oracle
- outlook
- thebat
- tbirdconfig
- powerpnt
- onenote
- dbeng50
- dbsnmp
- ocomm
- xfssvccon
- mspub
- msaccess
- infopath
- visio
- steam
- isqlplussvc
- wordpad
- agntsvc
- excel
- synctime
- mydesktopservice
- ocautoupds
- mydesktopqos
- thunderbird
- firefox
- sqbcoreservice
Revil Sodinokibi: Geographical Distribution
Sodinokibi’s target victims are geographically distributed with a concentration in the US, India and Europe.
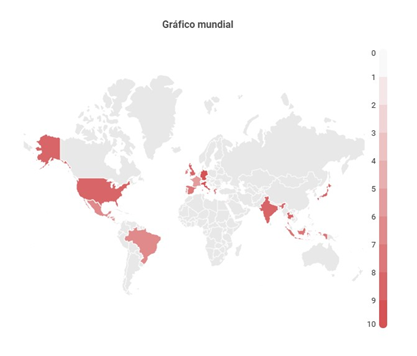
It is highlighted and pointed out that Eastern European countries are not the focus of attention.
Revil Sodinokibi: IoC
Below are the IoCs of the ransowmare Sodikinobi :
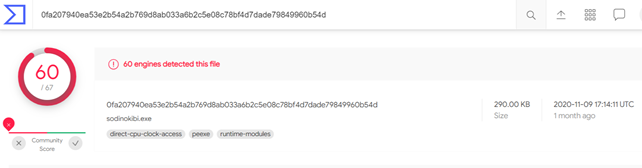
https://www.virustotal.com/gui/file/0fa207940ea53e2b54a2b769d8ab033a6b2c5e08c78bf4d7dade79849960b54d/detection
- MD5 fb68a02333431394a9a0cdbff3717b24
- SHA-1 1399bf98a509adb07663476dee7f9fee571e09f3
- SHA-256 0fa207940ea53e2b54a2b769d8ab033a6b2c5e08c78bf4d7dade79849960b54d
Filled IoC
The version of the Revil ransomware handled and analysed by Swascan during a DataBreach was found to be a customised variant of the ransomware in question. Specifically:
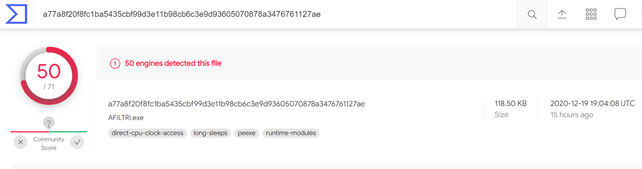
- MD5 f3b181a01ab21edca3ec193741676dec
- SHA-1 318021d9f68b87de16e7ddf2a19ea08031fc4af2
- SHA-256 a77a8f20f8fc1ba5435cbf99d3e11b98cb6c3e9d93605070878a3476761127ae
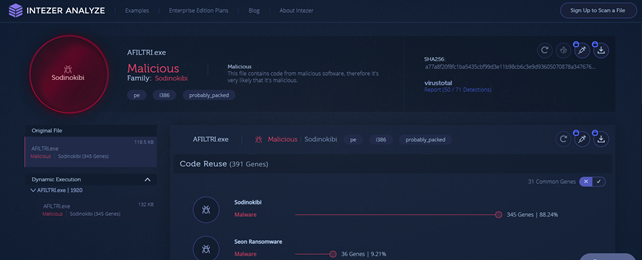
https://analyze.intezer.com/files/a77a8f20f8fc1ba5435cbf99d3e11b98cb6c3e9d93605070878a3476761127ae
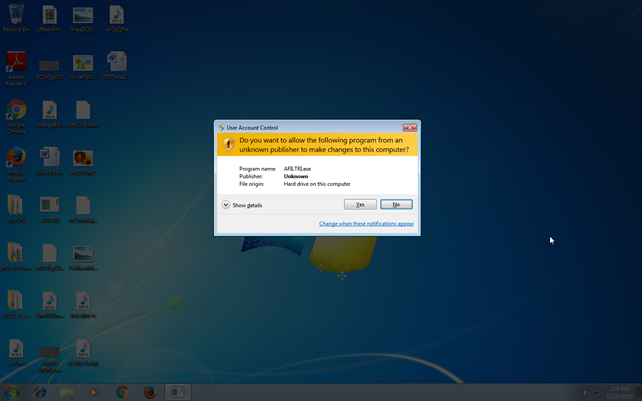
Payload Analysis
Analisi Minacce
Threat Identifiers (15 rules, 26 matches)
| Severity | Category | Operation | Count | Classification |
| 5/5 | Antivirus | Malicious content was detected by heuristic scan | 3 | – |
| 5/5 | Persistence | Writes to Master Boot Record (MBR) | 1 | – |
| 5/5 | Reputation | Known malicious file | 1 | – |
| 5/5 | YARA | Malicious content matched by YARA rules | 1 | – |
| 4/5 | User Data Modification | Modifies content of files | 1 | Ransomware |
| 4/5 | User Data Modification | Renames files | 1 | Ransomware |
| 3/5 | Network Connection | Connects to a CMS hoster | 1 | – |
| 2/5 | System Modification | Changes the desktop wallpaper. | 1 | – |
| 2/5 | Anti Analysis | Tries to detect virtual machine | 1 | – |
| 1/5 | Hide Tracks | Writes an unusually large amount of data to the registry | 1 | – |
| 1/5 | Mutex | Creates mutex | 1 | – |
| 1/5 | System Modification | Modifies application directory | 3 | – |
| 1/5 | System Modification | Creates an unusually large number of files | 1 | – |
| 1/5 | Network Connection | Connects to HTTPS server | 8 | – |
| 0/5 | Discovery | Enumerates running processes | 1 | – |
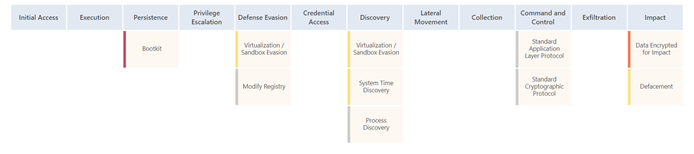
MITRE ATT&CK™ Matrix
Network Analysis
| Total Sent: 6.31 KB |
| Total Received: 15.08 KB |
| 1 ports: 443 |
| 8 contacted IP addresses |
| 0 URLs extracted |
| 0 files downloaded |
| 0 malicious hosts detected |
DNS
| 0 DNS requests for 0 domains |
| 0 nameserver contacted |
| 0 total requests returned errors |
HTTP/S
| 8 URLs contacted, 8 servers |
| 8 sessions, sending 6.31 KB, receiving 15.08 KB |

Hosts di Destinazione
Hosts Destinazione:
- dinslips.se
- airconditioning-waalwijk.nl
- babcockchurch.org
- ymca-cw.org.uk
- stoeberstuuv.de
- whyinterestingly.ru
- daniel-akermann-architektur-und-planung.ch
- slashdb.com
Virtual Machine Information
| Name | win7_64_sp1 |
| Description | |
| Architecture | x86 64-bit |
| Operating System | Windows 7 |
| Kernel Version | 6.1.7601.17514 (3844dbb9-2017-4967-be7a-a4a2c20430fa) |
| Network Scheme Name | Local Gateway |
| Network Config Name | Local Gateway |
Analyzer Information
| Analyzer Version | 3.2.2 |
| Dynamic Engine Version | 3.2.2 / 2020-06-03 06:06 (UTC+2) |
| Static Engine Version | 1.3.0 / 2020-06-03 08:06 (UTC+2) |
| Local AV Version | AVCORE v2.1 Linux/x86_64 11.0.1.19 (January 14, 2020) |
| Local AV Database Update Release Date | 2020-12-20 02:51:49+00:00 |
| VTI Ruleset Version | 3.6 |
| YARA Built-in Ruleset Version | 1.5 |
| Analysis Report Layout Version | 7 |
Software Information
| Adobe Acrobat Reader Version | 10.0.0 |
| Microsoft Office | 2010 |
| Microsoft Office Version | 14.0.4762.1000 |
| Internet Explorer Version | 8.0.7601.17514 |
| Chrome Version | 58.0.3029.110 |
| Firefox Version | 25.0 |
| Flash Version | 11.2.202.233 |
| Java Version | 7.0.450.18 |
System Information
| Sample Directory | C:\Users\5p5NrGJn0jS HALPmcxz\Desktop |
| Computer Name | XDUWTFONO |
| User Domain | XDUWTFONO |
| User Name | 5p5NrGJn0jS HALPmcxz |
| User Profile | C:\Users\5p5NrGJn0jS HALPmcxz |
| Temp Directory | C:\Users\5P5NRG~1\AppData\Local\Temp |
| System Root | C:\Windows |
How to defend yourself
It is possible to protect and defend one’s infrastructure from ransomware attacks through the adoption of a proper Cyber Security Framework.
Preventive security
Technological risk analysis:
Human Risk Analysis
- Phishing Simulation
- Smishing Simulation
- Training and Awareness
Organisational Risk Analysis
- ICT Security Assessment
- GDPR Assessment
Proactive Safety
Predictive Security
- Domain Threat Intelligence
- Cyber Threat Intelligence




